Attending conferences is a crucial way our staff can keep up to date with cutting-edge research, be introduced to important new ideas and perspectives, and help inspire and support the next generation of cyber security professionals. Our ID Cyber Solutions Conference Report series aims to showcase some exciting and ground breaking ideas presented at these events.
Report by Alice, Cyber Essentials Assessor and Technical Editor
On Saturday, 5th November 2022, I attended G3C, a student-run conference at Glasgow Caledonian University, now in its second year. 250 tickets were sold for the event, with attendees including industry professionals, recent university graduates, current students, and interested members of the public.
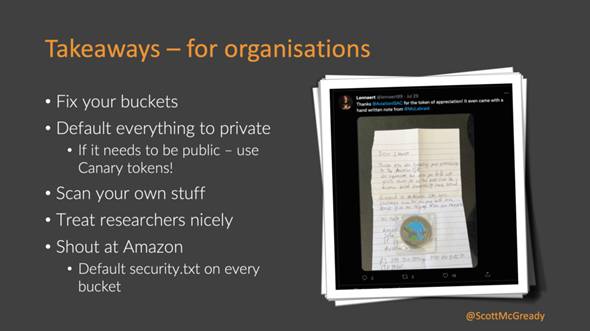
The conference ran four separate tracks—three presentation tracks and a workshop track focusing on lockpicking—so I could not attend every talk. However, the track in the main auditorium was live-streamed and uploaded to YouTube so that I could catch up on a few of the missed talks after the event. After an introduction from Dominik Hanlon (president of the Glasgow Caledonian Ethical Hacking Society), I made my way to Scott McGready’s talk ‘There’s a hole in your bucket’. Scott revealed that one of his hobbies is ‘bucket-hunting’—checking online repositories (like AWS S3 buckets) that companies or individuals have made publicly available and alerting the company if the data contained within should be privately stored. He provided several examples of buckets, freely searchable by the general public, that included HR phone call recordings, passwords and credit card information, and private email conversations before going on to advise on bucket security, how researchers can responsibly disclose that a company’s data is freely available, and how a company could best respond to a disclosure.
Next, I attended Gemma Craig’s talk ‘Nursing to cyber security’. After 14 years as a nurse, Gemma transitioned into a career in cyber security, including roles in the SOC (Security Operations Centre) and Incident Response. She highlighted the significant similarities between her nursing and cyber security careers, helping her audience see the value of transferable skills and understand how someone with a seemingly different professional background can quickly pick up critical cyber security skills. This was a very engaging talk, full of personal touches and good humour, and it helped me think of additional ways to explain technical ideas to those who don’t work in a technical field. Dave McKenzie followed Gemma with a presentation on ‘Digital Deception’. This talk encouraged the audience to consider the usefulness of honeypots and canary tokens and how to add them effectively into a network, helping companies quickly identify when an unauthorised individual (whether external or an insider threat) has accessed the system. Using a live demonstration involving the audience and a series of QR codes, Dave showed how easily canary tokens could be set up and the information they could pass to the token owner. This was undoubtedly a talk that made the audience think about the security of their networks and ways to protect them better.

After the lunch break, I attended Sean Wright’s presentation on ‘Software supply chain woes’, which pointed out security issues resulting from using existing libraries or packages in applications. Sean showed how some packages contained vulnerabilities yet were still incorporated, unchecked, into large numbers of applications—a talk of interest to anyone relying on pre-built libraries or packages, anyone using plug-ins, or anyone asking third parties to develop applications for them.
Andy Gill’s closing keynote, ‘Expanding your horizons’, comprised a whistle-stop tour through his cyber security career, including tips and tricks on avoiding burnout and career progression (and an array of impressive photographs, the hobby being one of his ways to avoid burnout). The talk was very well-received by current or recent students in the audience hoping to begin in the industry on the right footing and was a fitting end to a student-led event.
After the event, I took the opportunity to use the YouTube recordings to catch up on one of the talks I missed—Gerard Barrett’s ‘To SOC Analyst… and Beyond!’. Gerard, like Gemma, discussed his transition into cyber security from a different industry (in his case, fraud investigation). However, the two talks had very different focuses, making them equally valuable. My main takeaways from Gerard’s presentation were the various ways that the cyber security community had shaped his career path, with a vast number of people offering him a wealth of friendly support and advice, and how he built his knowledge through the use of different online courses.
Other scheduled talks that I wasn’t able to attend were:
▪ David Edwards—The Darkness of Powers Hell (Powershell Abuse)
▪ Rory McCune—Wonder the world of container security
▪ Petros Wallden—Cyber Security In The Quantum Era
▪ Fred Crowson—Openbsd secure operating system for everyone
▪ Joshua Brown—”Kind of Blue” Working in SOC
▪ Eliot Bolster—Demo-Democracy Directly Doomed
Thanks to G3C and all the speakers for a fun and informative conference, and I look forward to using my new knowledge and ideas to support ID Cyber Solutions’ customers better.
